Massive iOS Exploit Kit 'Coruna' Spotted in Wild: Google Reveals 23 Flaws Used in Targeted Attacks
Google reveals 'Coruna' iOS exploit kit targeting iPhones from iOS 13 to 17.2.1 with 23 exploits. Used by surveillance vendor customer, Russian espionage group, and Chinese financial actor. Users urged to update.
Breaking: Powerful iOS Exploit Kit 'Coruna' Targets Millions of iPhones
Google's Threat Intelligence Group (GTIG) has uncovered a highly sophisticated exploit kit named 'Coruna' that targets iPhones running iOS versions 13.0 through 17.2.1. The kit contains 23 distinct exploits and five full exploit chains, making it one of the most comprehensive iOS attack tools ever seen in the wild.
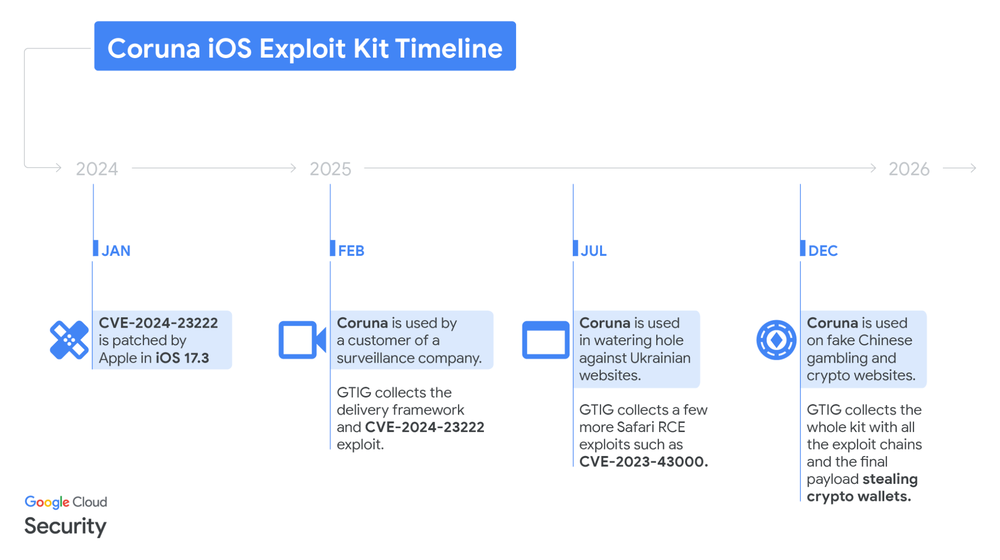
According to GTIG, Coruna was first detected in February 2025 and has already been used by at least three different threat actors. These include a customer of a commercial surveillance vendor, a suspected Russian espionage group (UNC6353), and a financially motivated group operating from China (UNC6691).
'This is an unprecedented collection of iOS exploits,' said a senior GTIG researcher who spoke on condition of anonymity. 'The rapid proliferation we observed suggests a thriving underground market for second-hand zero-day exploits.'
iPhone users are urged to update immediately to the latest iOS version, as Coruna is ineffective against current builds. For devices that cannot be updated, enabling Lockdown Mode provides enhanced protection.
Timeline of Discovery and Proliferation
GTIG first captured parts of a Coruna exploit chain in February 2025. The initial user was a customer of a surveillance firm—a pattern consistent with the commercial spyware ecosystem.
In mid-2025, the same exploit kit was deployed in watering hole attacks targeting Ukrainian users. GTIG attributes these attacks to UNC6353, a known espionage group linked to Russian interests.
Later, GTIG retrieved the complete exploit kit after it was used in broad-scale campaigns by UNC6691, a financially motivated actor based in China. 'How this kit changed hands so quickly remains unclear, but the evidence points to active trading of advanced offensive capabilities,' the researcher added.
Background: How Coruna Works
Coruna is delivered via a custom JavaScript framework that uses simple obfuscation techniques, including XOR-encoded strings and integer arithmetic. The script first fingerprints the target device to determine the exact iPhone model and iOS version.

Based on the fingerprint, it loads a WebKit remote code execution (RCE) exploit, followed by a pointer authentication code (PAC) bypass. The exploit kit contains 23 total exploits—some using non-public techniques and mitigation bypasses never before seen in the wild.
Google has added all identified malicious domains to Safe Browsing and shared technical details with Apple. 'We are releasing this research to raise awareness and help the security community defend against these advanced threats,' GTIG stated.
What This Means for iPhone Users
The most immediate action users can take is to update to the latest version of iOS. Coruna does not work against current builds, and Apple has patched many of the vulnerabilities used in the kit.
For those running older iPhones that cannot upgrade, Lockdown Mode is highly recommended. This feature severely restricts device functionality, making exploitation much harder even if a vulnerability exists.
Beyond individual users, this discovery highlights a troubling trend: advanced exploit capabilities are becoming commoditized. 'The same exploits used to target dissidents and journalists can now be found in the hands of cybercriminals and nation-state actors,' noted the GTIG researcher. 'This changes the threat landscape for everyone.'
Google continues to monitor Coruna-related activity and will update Safe Browsing as new threats emerge. Organizations with high-risk users should consider additional endpoint detection and network monitoring for signs of exploit delivery.
This is a breaking security story. Check back for updates.